AI-Powered M&A Due Diligence
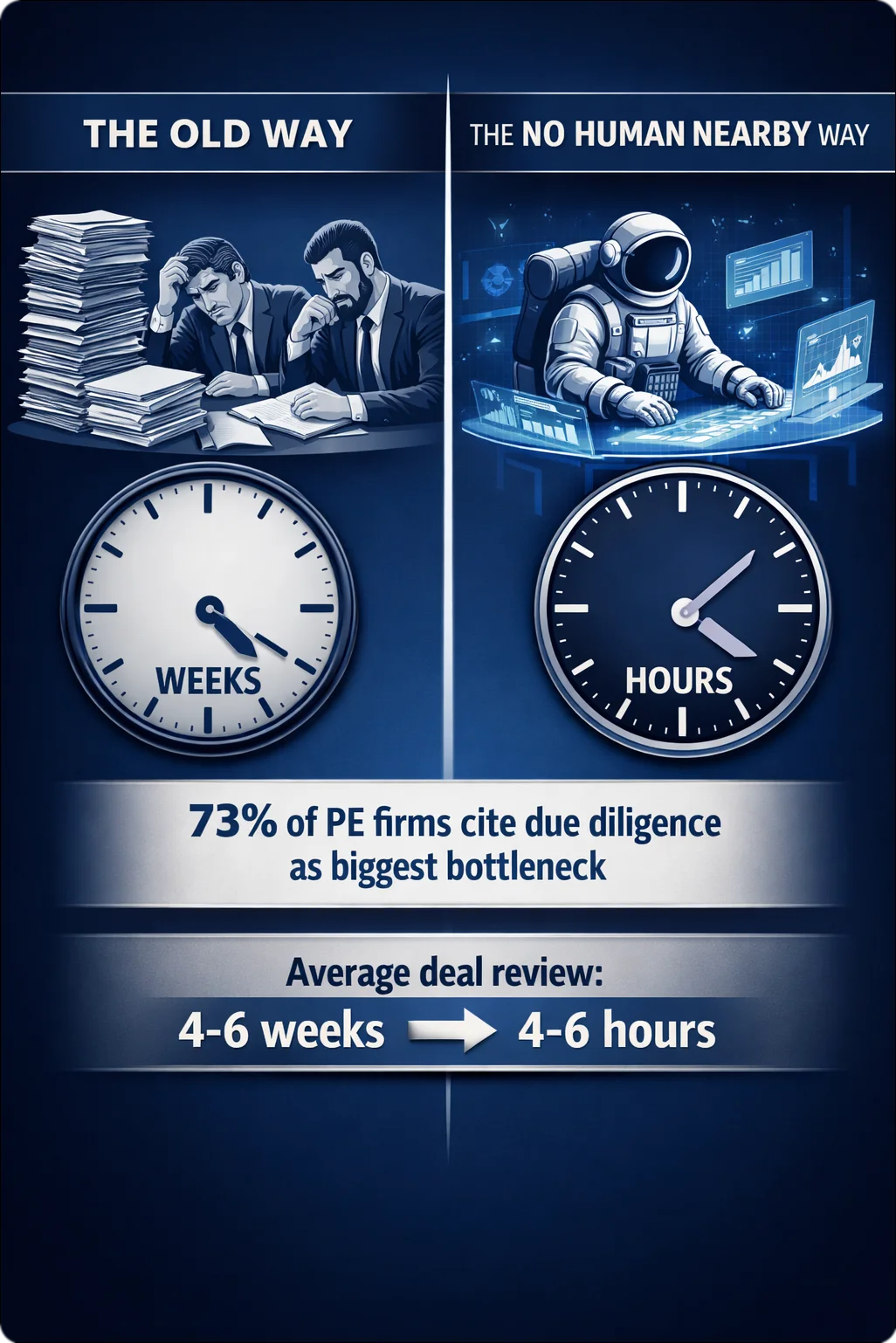
Deal Review in Hours,
Not Weeks
An additive intelligence layer alongside Intralinks, Datasite, and Firmex. Keep your VDR. Add the noise cancellation. Lawyers read only the things that matter.
Institutional-grade AI analysis for PE firms and M&A advisors.
Surface contract risks across entire portfolios before closing.
Sovereign architecture. Documents route to dedicated infrastructure under our exclusive control via secure tunnel. Enterprise AI at small-firm prices.